Why Physical and Cyber Threats Can't be Treated Separately
When Ankur Agurwas used a stolen access badge to illegally enter a New Jersey business and inserted a keylogger into their computer system, was the problem a physical one or a digital one?
 Whose responsibility was the data breach when he stole personal data from the ‘Emerging Technologies’ team? Front of house security or the cyber team? Is Agurwas a hacker or a burglar? These questions don’t make sense because of course the answer is, both. But they illustrate a major flaw in our thinking about ‘Infosec’. If we separate responsibility into silos, we create vulnerabilities.
Whose responsibility was the data breach when he stole personal data from the ‘Emerging Technologies’ team? Front of house security or the cyber team? Is Agurwas a hacker or a burglar? These questions don’t make sense because of course the answer is, both. But they illustrate a major flaw in our thinking about ‘Infosec’. If we separate responsibility into silos, we create vulnerabilities.
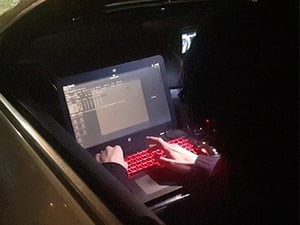
Photo: WFF's Head of Cyber Solomon Gilbert tests vulnerabilities in an office wifi network from a car across the street.
Omni-channel criminals
This organisation was guarding against a data breach via cyber attack and a burglary via physical entry; but criminals don’t think in these siloed terms any more. In the 2020s we have generations of criminals who have grown up in a digital world. They understand the value of data and possess knowledge of how to steal it in their criminal organisations. But they also have knowledge and experience of breaking physical security systems like alarms or entry controls and they are experts in people or personnel manipulation (or as it’s now called: social engineering).
The recent discovery of Iranian hackers’ videos showed them using a combination of hacking OSINT and spear phishing. The recent attack on high profile Twitter users may have been a hack, it may have involved an insider, it certainly used social engineering techniques to turn the breach into money. These combinations of attack vectors are far more dangerous than any single surface.
What is the solution?
There are solutions which could have prevented the New Jersey data breach. For example, software which can correlate access cards with login attempts; even comparing typing speed of the person who should be logging in with the one who is actually logging in. But if you’re not expecting that type of attack you will not know what kind of controls to put in place.
The most effective and often low cost option for many organisations’ security teams is to adopt a holistic security mindset. With an overview of data processes, access controls, through physical, cyber, social engineering and importantly staff training; everyone needs to be communicating with each other. Criminals are already doing this, if we continue to work in silos, we’re allowing them to continually undermine us without the means to counter it.
Video: WFF's Holistic Threat Assessment team test vulnerabilities in an office WiFi network from a car park 100 yards from the building.