Ransomware warning issued to MSPs and clients by US Secret Service
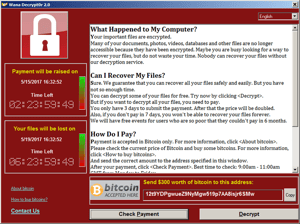 There has been such a big increase in hacks of managed service providers (MSPs) recorded by the US Secret Service that they have issued a warning. They report that hackers are breaching MSPs to orchestrate ransomware attacks, point-of-sale intrusions, and business email compromise (BEC) scams on their clients. The Secret Service have issued best practice guidance which includes advice to proactively conduct education and training for staff.
There has been such a big increase in hacks of managed service providers (MSPs) recorded by the US Secret Service that they have issued a warning. They report that hackers are breaching MSPs to orchestrate ransomware attacks, point-of-sale intrusions, and business email compromise (BEC) scams on their clients. The Secret Service have issued best practice guidance which includes advice to proactively conduct education and training for staff.
Hackers using MSPs as gateways into other companies.
MSPs provide remote management software to companies. They are connected to the server-client software. If an attacker gains access to the server aspect of the MSP, they will have full control of all software clients. This means all companies are at risk; from the smallest ones which rely on simple file-sharing systems to large international companies with MSPs that manage entire computer fleets.
This is particularly concerning considering that there is an increased reliance on managed service providers due to Covid-19 as more and more people are working remotely. Indeed the Global Investigations Operations Centre arm of the US Secret Service sent out an alert in June (2020). It warned of an increase in hackers breaching MSPs and using them to enter the internal networks of companies’ clients. Once in, they cause financial and relational damage by deploying ransomware, creating business email compromise scams and attacking point-of-sale systems.
MSPs major targets for hackers
ConnectWise, one of the largest distributors of MSPs has been repeatedly targeted by hackers who deployed ransomware. This is believed to have triggered the second security alert in relation to MSPs. The first was in 2018 which warned companies and MSP vendors about state-sponsored hackers who were breaching cloud-based service providers (a form of MSP). Suspicion has it that the criminal gang behind the initial hacks were state-sponsored and from China. However, currently, the attacks are perpetrated by members of the public who have formed cyber gangs.
What should companies be doing?
As well as effective training, the warning underlines the need for organisations to include 3rd party service providers in their penetration testing routines. We Fight Fraud have previously found major vulnerabilities in 3rd party software which would compromise the security of significant organisations. An effective security strategy must recognise that 3rd party suppliers are a potential criminal entry point.